A Simple Time & Material Platform for the Job Site
Increase your team's productivity by digitizing your field data today.
GET STARTED TODAY
Increase your team's productivity by digitizing your field data today.
GET STARTED TODAY
Gain insight into project performance and mitigate delays and costs overruns.
Learn more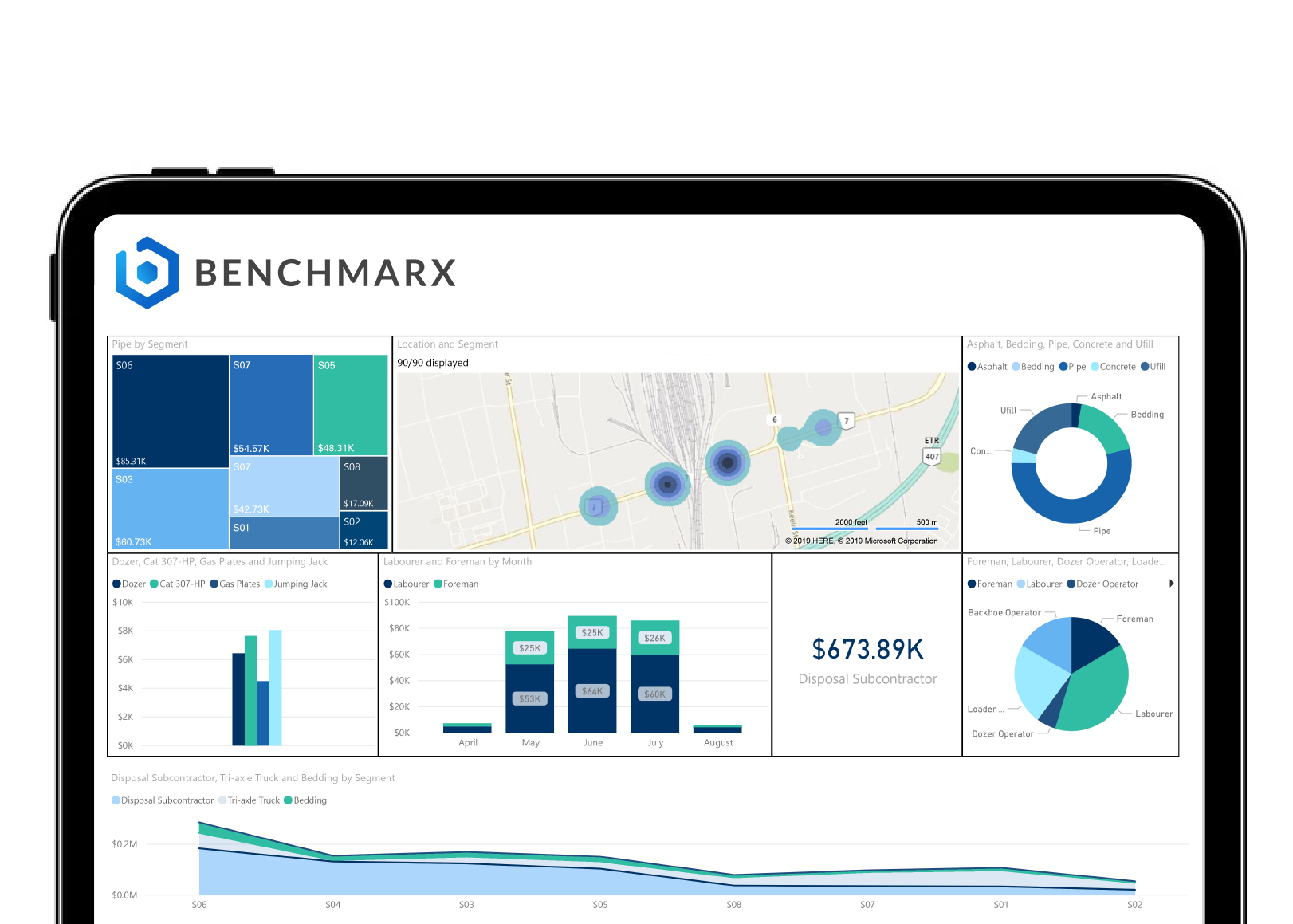
Helping owners, general contractors, and subcontractors digitize their field data.






BenchMarx's data-driven solutions are transforming the way construction teams work. Watch what our customers appreciate most.
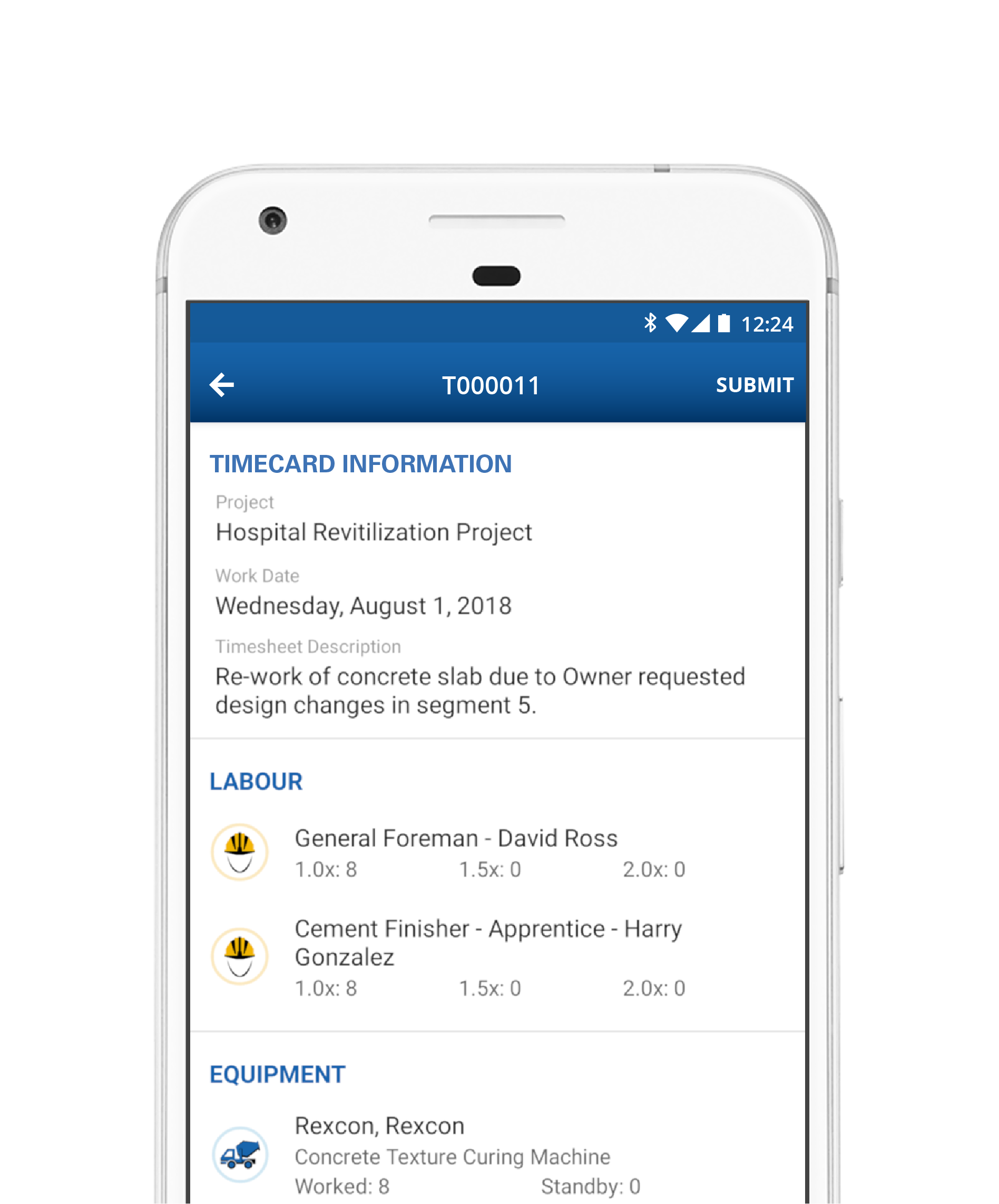
Streamline your payroll process and submit timecards from the field in seconds.
Keep track of production rates, labor hours, pictures and field notes on any mobile device.
Learn more
Subs, GC's, and Owners can each view field data across all projects through a seamless and transparent system.
Our cloud-based solutions will integrate with your existing payroll system, allowing foremen to instantly submit timecards.
A paperless solution to reduce risk and improve cost recovery of changes on the job site.

Track labor, material, equipment and sub-tier vendors on a simple yet powerful app, and never lose documentation again.
Create flawless invoices, attach supporting documentation, and collect digital approvals through our cloud-based system.
Take advantage of our full set of features to significantly improve turnaround time and increase cash flow.
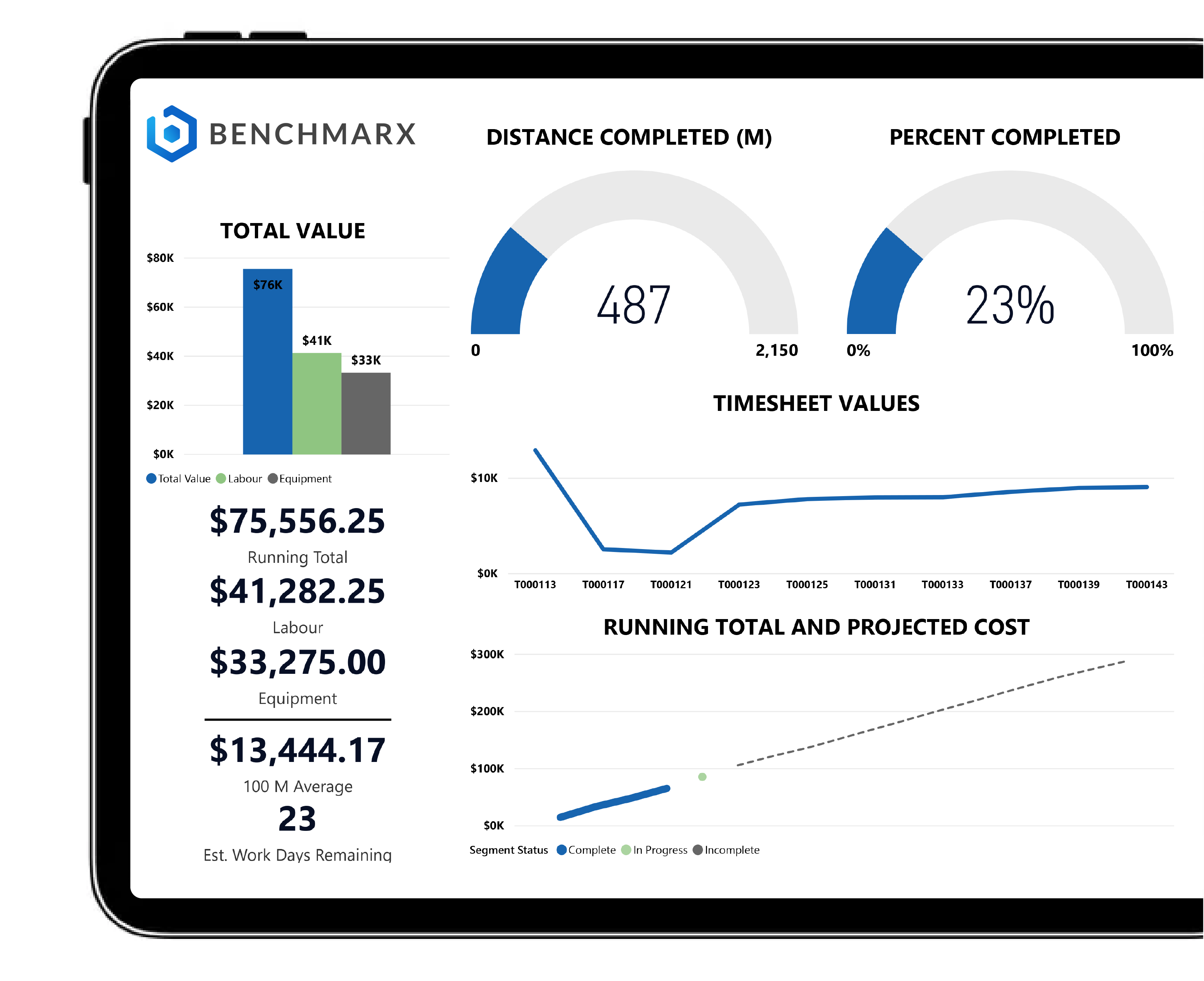
Dig into details with end-to-end visibility from the field to the office.
Custom dashboards provide real-time insights into productivity, production rates, budgets and unit rates.
Use your data to increase productivity and identify problem areas so that you can get ahead or get back on track.
Identify outliers and create accurate forecasts using predictive analytics.